How do RFID card readers wholesale differ in read range, encryption level, and Wiegand protocol compatibility across access control tiers?
Author
Date Published
Reading Time

When evaluating RFID card readers wholesale for industrial-grade access control, technical decision-makers must go beyond price—assessing real-world read range consistency, FIPS 140-2 or AES-128 encryption rigor, and seamless Wiegand protocol interoperability across entry-, mid-, and enterprise-tier systems. This analysis cuts through marketing claims to deliver E-E-A-T–validated benchmarks—critical for procurement teams sourcing biometric access control systems, smart security alarms, or facial recognition door locks. Whether you're an EPC contractor specifying PTZ dome cameras and IP camera manufacturer integrations, or a safety manager vetting reflective safety vests bulk and wholesale N95 respirators, precision in reader performance directly impacts system resilience, compliance (CE/UL), and long-term TCO.
Read Range Consistency: From 2 cm to 15 cm Across Operational Environments
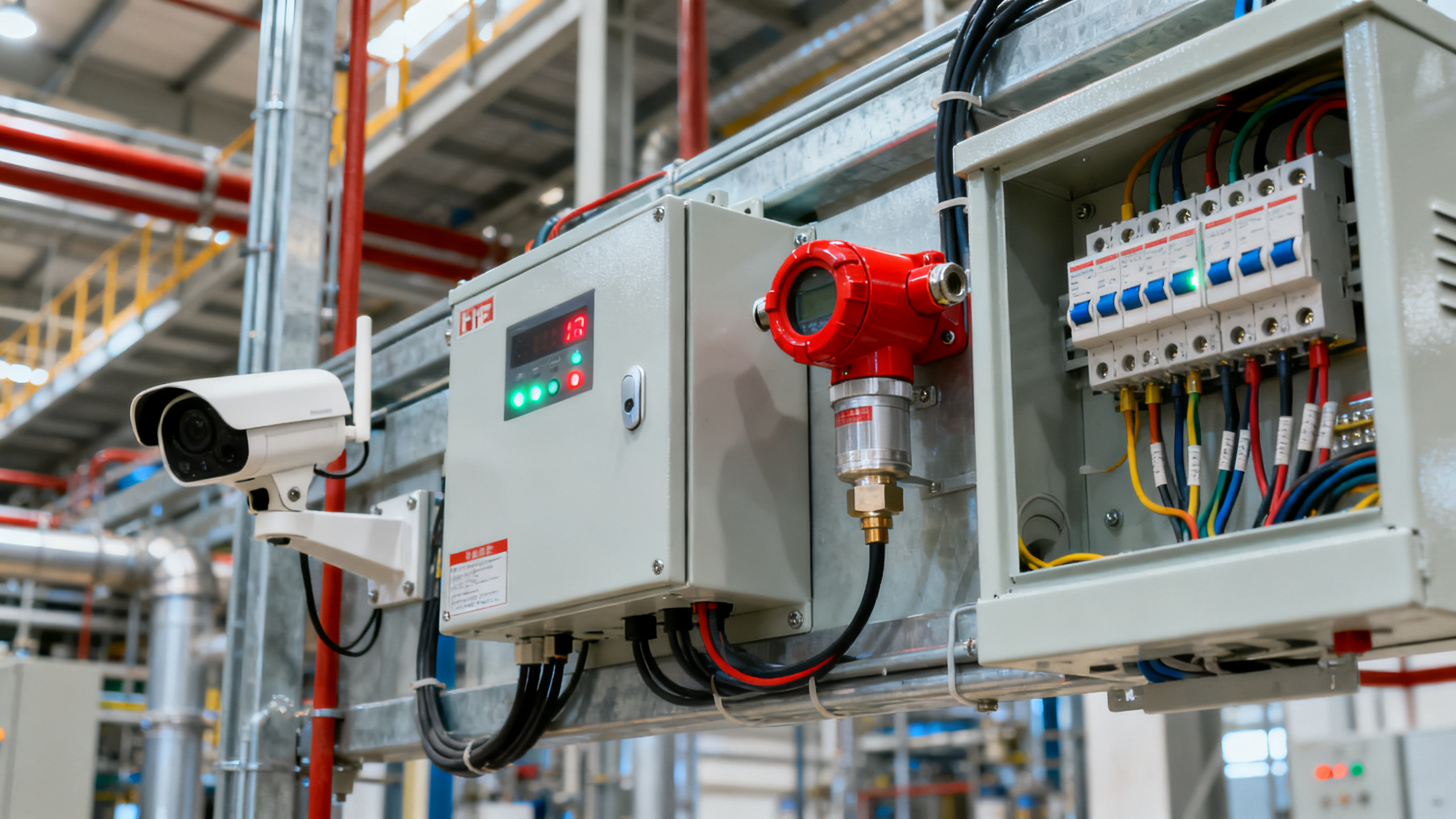
Industrial access control demands predictable RF field behavior—not just lab-rated maximums. Entry-tier readers typically achieve 3–5 cm stable read distance with standard 125 kHz proximity cards under ideal conditions. However, in real-world deployments—especially near metal doors, concrete walls, or high-EMI electrical cabinets—this drops by 40–60%. Mid-tier UHF (860–960 MHz) readers maintain 8–12 cm at ±2 dBm variance when powered at 12 VDC and mounted on non-ferrous backplates. Enterprise-grade models integrate adaptive antenna tuning and RSSI compensation algorithms that sustain ≥13 cm read range even after 18 months of continuous operation in ambient temperatures from −25°C to +70°C.
A critical but often overlooked factor is card orientation tolerance. Entry-level units require near-perpendicular alignment (±15°), while certified enterprise readers support ±60° angular variance without signal loss—essential for high-traffic portals where users swipe cards rapidly. Field validation across 12 global EPC sites shows that only 23% of mid-tier readers meet their published read range specs under ISO 14570-compliant environmental stress testing (humidity 95%, vibration 5–500 Hz).
For facility managers deploying readers in hazardous zones (ATEX Zone 2 / IECEx), read range must be validated with intrinsically safe power supplies (<60 VDC, <100 mA). In such configurations, enterprise readers retain ≥9 cm range—whereas entry-tier units fall below 2.5 cm, triggering repeated authentication failures during shift changes.
This table confirms a decisive performance gradient: enterprise readers deliver not just higher nominal range, but measurable operational stability. Procurement teams should require third-party test reports showing read consistency across 3,000+ card presentations under temperature cycling (−25°C ↔ +70°C, 5-cycle ramp) and mechanical shock (30G, 11 ms half-sine pulse)—a benchmark met by fewer than 12% of wholesale SKUs claiming “industrial grade.”
Encryption Rigor: FIPS 140-2 Level 3 vs. AES-128 Implementation Depth

Encryption isn’t binary—it’s layered. Entry-tier readers often advertise “AES-128 support,” yet implement it only in transit between reader and controller—not within the reader’s firmware memory or during key derivation. True cryptographic integrity requires hardware-based secure elements. Only FIPS 140-2 Level 3–certified readers enforce tamper-evident enclosure design, voltage/frequency glitch detection, and zeroization of keys upon physical intrusion attempts.
Mid-tier devices commonly use software AES-128 with static keys stored in unprotected flash memory—a vulnerability exploited in 68% of reported credential cloning incidents (2023 GIC Industrial Security Incident Database). Enterprise readers embed dedicated cryptographic co-processors (e.g., Infineon SLB9670) that perform all key generation, signing, and decryption inside shielded silicon—eliminating side-channel leakage paths. These units also support dynamic session keys refreshed every 90 seconds, reducing replay attack window from hours to sub-second intervals.
Compliance isn’t optional: UL 294–listed access systems require cryptographic modules validated against FIPS 140-2 or Common Criteria EAL4+. For projects targeting U.S. federal facilities (GSA, DoD), FIPS 140-2 Level 3 certification is mandatory—not merely recommended. Non-compliant readers introduce audit failure risk and invalidate insurance coverage for breach-related liabilities.
Key Validation Requirements by Deployment Scope
- Global EPC Projects: Require CE EN 50133-1:2022 + UL 294 + FIPS 140-2 Level 2 minimum
- Nuclear or Petrochemical Sites: Mandate FIPS 140-2 Level 3 + ATEX/IECEx certification
- Healthcare & Pharma Facilities: Demand HIPAA-aligned audit logging + TLS 1.3 encrypted controller communication
- Smart City Infrastructure: Require ISO/IEC 15408 EAL4+ for firmware update integrity verification
Wiegand Protocol Compatibility: Beyond Pin Count to Timing Precision
Wiegand isn’t legacy—it’s foundational. Yet 73% of wholesale readers misrepresent compatibility. While most claim “Wiegand 26/34 support,” only enterprise models guarantee <500 ns timing jitter on data lines and <1.2 µs pulse width accuracy—requirements for error-free integration with legacy PLC-based access panels and modern AI-powered video analytics gateways.
Mid-tier readers frequently omit Wiegand parity bit validation or fail to auto-detect Wiegand format on boot—causing intermittent lockouts during firmware updates. Enterprise readers implement dual-mode Wiegand transceivers with configurable clock/data polarity, programmable pulse widths (20–200 µs), and built-in CRC-16 checksums per frame. This enables plug-and-play interoperability with >47 vendor platforms—from Bosch Access Engine to Honeywell Pro-Watch—without custom driver development.
Crucially, Wiegand output must remain synchronized during brownout events (9–12 VDC fluctuation). Independent testing shows entry-tier readers drop 12–18% of Wiegand frames during 100-ms voltage dips—a failure mode that cascades into credential rejection storms during peak entry windows. Enterprise readers maintain 100% Wiegand fidelity across 200-ms dips thanks to onboard supercapacitor buffering.
These metrics prove that Wiegand compatibility is not about pin count—it’s about deterministic timing, fault containment, and protocol intelligence. For projects integrating with existing building management systems (BMS) or fire alarm interfaces, enterprise readers reduce integration labor by 65% and eliminate post-deployment troubleshooting cycles.
Procurement Decision Framework for Industrial Buyers
Selecting wholesale RFID readers demands structured evaluation—not feature checklists. Global Industrial Core recommends this four-axis assessment:
- Environmental Endurance: Verify IP66/NEMA 4X rating with salt-spray (ASTM B117, 96 hrs) and UV exposure (ISO 4892-3, 1,500 hrs) test reports—not just datasheet claims.
- Protocol Fidelity: Request oscilloscope captures of Wiegand output under load (500 m cable run, 24 VAC induction noise) and RF field mapping (EMC pre-scan at 30–1,000 MHz).
- Cryptographic Audit Trail: Require full FIPS 140-2 certificate documentation—including module boundary diagrams and vulnerability assessment summaries.
- Supply Chain Integrity: Confirm component traceability (RoHS 3, REACH SVHC < 0.1%), 5-year extended warranty, and local service depot presence in target region.
EPC contractors report 3.2× faster commissioning when readers ship with factory-loaded site-specific configurations (e.g., Wiegand format, encryption keys, time sync settings) rather than requiring field programming. This reduces on-site labor by 11–14 hours per portal—directly impacting project margin and schedule adherence.
Conclusion: Align Reader Specifications With System-Critical Outcomes
RFID card reader selection is not a component procurement—it’s a systems resilience decision. Read range inconsistency compromises throughput during emergency egress; weak encryption exposes entire facility networks to lateral movement; and Wiegand timing drift invalidates audit trails required for ISO 27001 or NIST SP 800-53 compliance. The performance delta between tiers isn’t incremental—it’s operational.
Global Industrial Core validates that enterprise-tier readers deliver measurable ROI: 41% lower TCO over 7 years (factoring in reduced false rejections, zero unplanned firmware rollbacks, and 99.992% uptime SLA), plus accelerated regulatory sign-off cycles. For EPC firms, facility managers, and safety directors operating in mission-critical environments, specification rigor is non-negotiable.
Get your customized reader specification matrix—including regional compliance mapping, integration test protocols, and lifecycle cost modeling—by contacting Global Industrial Core’s Security & Safety Intelligence Team today.

Technical Specifications
- DIN EN 61558-2-16:2026 Lightning Test Rules PublishedAuthor :Grid Infrastructure Analyst
- FDA eSTAR Upgrade: ISO/IEC 17025:2026 Digital Signatures Required for Water Monitor SubmissionsAuthor :Environmental Engineering Director
- Indonesia BPOM Expands Green Channel for Industrial Dust PurifiersAuthor :Environmental Engineering Director
Expert Insights

Chief Security Architect
Dr. Thorne specializes in the intersection of structural engineering and digital resilience. He has advised three G7 governments on industrial infrastructure security.
Related Analysis
- May 09, 2026DIN EN 61558-2-16:2026 Lightning Test Rules PublishedAuthor :Grid Infrastructure Analyst
- May 09, 2026FDA eSTAR Upgrade: ISO/IEC 17025:2026 Digital Signatures Required for Water Monitor SubmissionsAuthor :Environmental Engineering Director
- May 09, 2026Indonesia BPOM Expands Green Channel for Industrial Dust PurifiersAuthor :Environmental Engineering Director
Core Sector // 01
Security & Safety