Security & Safety standards that affect product acceptance
Author
Date Published
Reading Time

In industrial procurement, product acceptance depends on more than price or availability—it hinges on strict compliance, traceable performance, and risk control. Security & Safety standards shape every stage of evaluation, from design verification to site approval, making them essential for quality control and safety managers who must prevent failure, ensure regulatory alignment, and protect long-term operational reliability.
For quality control and safety managers, the key question is usually not whether standards matter, but which Security & Safety standards actually affect acceptance, how to verify them efficiently, and where hidden compliance gaps can delay installation or expose the organization to liability. In most industrial settings, product acceptance is determined by a combination of regulatory requirements, end-user specifications, installation environment, and the credibility of the supplier’s testing evidence.
This means a product can be technically functional and still fail acceptance if its markings are incomplete, its certification is not recognized in the destination market, its test reports are outdated, or its documentation does not match the delivered configuration. For teams responsible for release decisions, understanding the acceptance impact of Security & Safety standards is therefore a practical control issue, not just a compliance topic.
What quality and safety teams are really trying to confirm before accepting a product
When users search for Security & Safety standards that affect product acceptance, they are usually trying to answer a high-stakes operational question: can this product be approved, installed, and used without creating regulatory, safety, or contractual risk? They need a decision framework, not a generic list of standards.
For quality control personnel, acceptance depends on objective evidence. They want to know whether the product complies with the right standard for the intended use, whether the compliance is current and traceable, and whether the product delivered is identical to the tested product. Small inconsistencies in labels, materials, enclosure ratings, or electrical characteristics can invalidate acceptance even when the supplier claims conformity.
Safety managers often focus on a broader risk picture. They need to confirm that the product will not introduce hazards during installation, commissioning, maintenance, or abnormal operation. That includes electrical safety, fire behavior, explosion risk, emergency performance, access control reliability, machine guarding, and functional safety where applicable.
In practice, these teams are asking four things. First, which standards are mandatory in this application and region? Second, what proof is acceptable? Third, what defects or omissions commonly lead to rejection? Fourth, how can they evaluate products faster without lowering control quality?
Which Security & Safety standards most often influence product acceptance
Not all standards carry the same acceptance weight. Some are legally required, some are customer-mandated, and some act as strong trust signals during technical evaluation. The products covered under Security & Safety can vary widely, from industrial cameras and access control devices to emergency shutdown components, detectors, protective enclosures, cables, and machine safety assemblies. Because of that, acceptance should be mapped against product category and installation environment.
At the broadest level, ISO standards often affect management credibility and process maturity. For example, ISO 9001 supports confidence in quality consistency, while ISO 45001 signals occupational health and safety management capability. These may not by themselves approve a product, but they can influence supplier qualification and reduce perceived risk during audits.
CE marking is critical for products entering the European Economic Area, but teams must remember that CE is not a standalone performance standard. It is a conformity framework linked to applicable directives or regulations, such as the Low Voltage Directive, EMC requirements, Machinery Regulation context, or ATEX where explosive atmospheres are involved. A CE mark without a valid Declaration of Conformity and technical backing should not be treated as sufficient acceptance evidence.
UL and other Nationally Recognized Testing Laboratory certifications are highly influential in North America, especially for electrical safety. In many facilities, UL listing or recognition can directly affect whether equipment is approved by inspectors, insurers, or end users. Similar importance applies to CSA, ETL, and other accepted certification schemes depending on jurisdiction and buyer requirements.
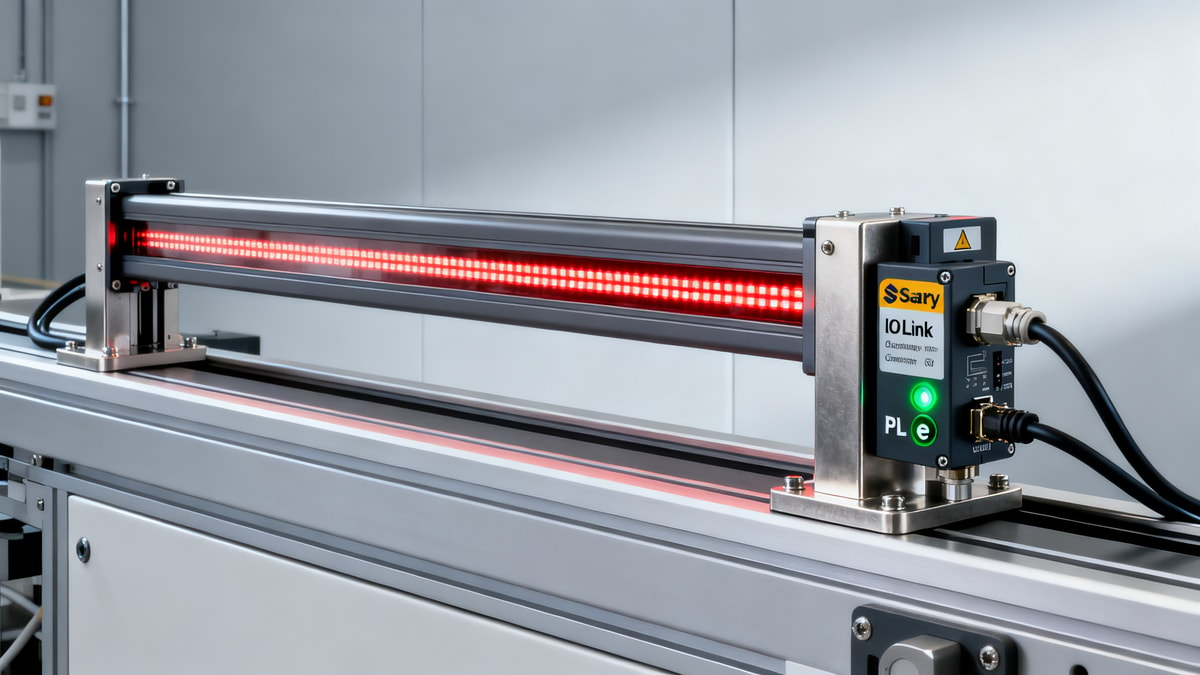
IEC standards often form the technical basis for product evaluation across industrial markets. IEC 60529 for IP ratings, IEC 61010 for safety requirements of measurement and control equipment, IEC 60204 for machine electrical equipment, and IEC 61508 or related functional safety standards can all affect acceptance decisions. In hazardous areas, IECEx and ATEX-related requirements are often decisive.
Security standards increasingly matter alongside traditional safety requirements. For network-connected industrial devices, cybersecurity expectations can influence acceptance, especially in critical infrastructure and regulated facilities. Standards and frameworks such as IEC 62443 may become part of technical approval because insecure devices can create operational and safety exposure, even if their physical design is compliant.
Fire performance standards also frequently affect acceptance. Depending on product type, this may include flame resistance, smoke emission, fire stopping, alarm performance, or emergency system reliability. In infrastructure, transport, energy, and public facilities, these requirements can override cost considerations because a failed fire compliance review can block an entire project milestone.
Why products fail acceptance even when suppliers claim compliance
A common procurement mistake is assuming that a certification logo, test summary, or supplier declaration automatically proves acceptance readiness. In reality, many products fail at the evidence-validation stage. The issue is usually not the absence of claims, but the weakness of supporting documentation.
One frequent problem is scope mismatch. A supplier may provide a valid certificate, but it applies to a different model, voltage range, material class, software revision, or enclosure configuration than the product being delivered. For quality teams, this is a major red flag because acceptance must apply to the exact delivered item, not a similar family reference.
Another issue is market mismatch. A product approved for one country may not be acceptable in another if the certification body, labeling method, or legal framework is different. This is especially relevant for multinational EPC projects where equipment sourced globally must still meet local approval rules at the installation site.
Expired, withdrawn, or superseded standards can also create hidden rejection risk. A supplier may have been compliant when the product was first designed, but if the applicable standard has changed and the end user specification references the newer edition, the product may require retesting, redesign, or documented gap assessment before acceptance.
Documentation inconsistency is another major cause of rejection. If the nameplate, user manual, declaration, test report, and packing label do not align, inspectors may suspend approval until the discrepancy is resolved. Even simple omissions such as missing warning labels, unclear installation limitations, or incomplete environmental ratings can trigger nonconformance reports.
Finally, some products fail because compliance exists only under laboratory conditions that do not reflect the application. A device may pass a test in a controlled setup but be unsuitable for vibration, corrosive exposure, washdown, temperature extremes, or electromagnetic disturbance in the field. Acceptance should therefore consider both formal certification and actual service suitability.
How to evaluate Security & Safety standards in a way that supports faster acceptance
The most effective acceptance process starts before the purchase order is issued. Quality and safety managers should define a standards matrix during specification development. This matrix should list mandatory regulations, recognized certification schemes, environmental performance requirements, documentation needs, and any site-specific safety conditions. Doing this early prevents late-stage arguments about what “compliant” means.
During supplier evaluation, ask for primary evidence, not just marketing claims. That usually includes certificates, Declarations of Conformity, accredited test reports where relevant, datasheets, installation manuals, traceability information, and change-control records. If software or firmware affects safety or security functions, version control should also be reviewed.
It is also useful to separate acceptance into three layers. The first is legal compliance: can the product legally enter and be used in the target market? The second is technical compliance: does it meet project and application requirements? The third is operational acceptability: will it perform safely and reliably in the real installation context? A product that passes only the first layer should not automatically clear final acceptance.
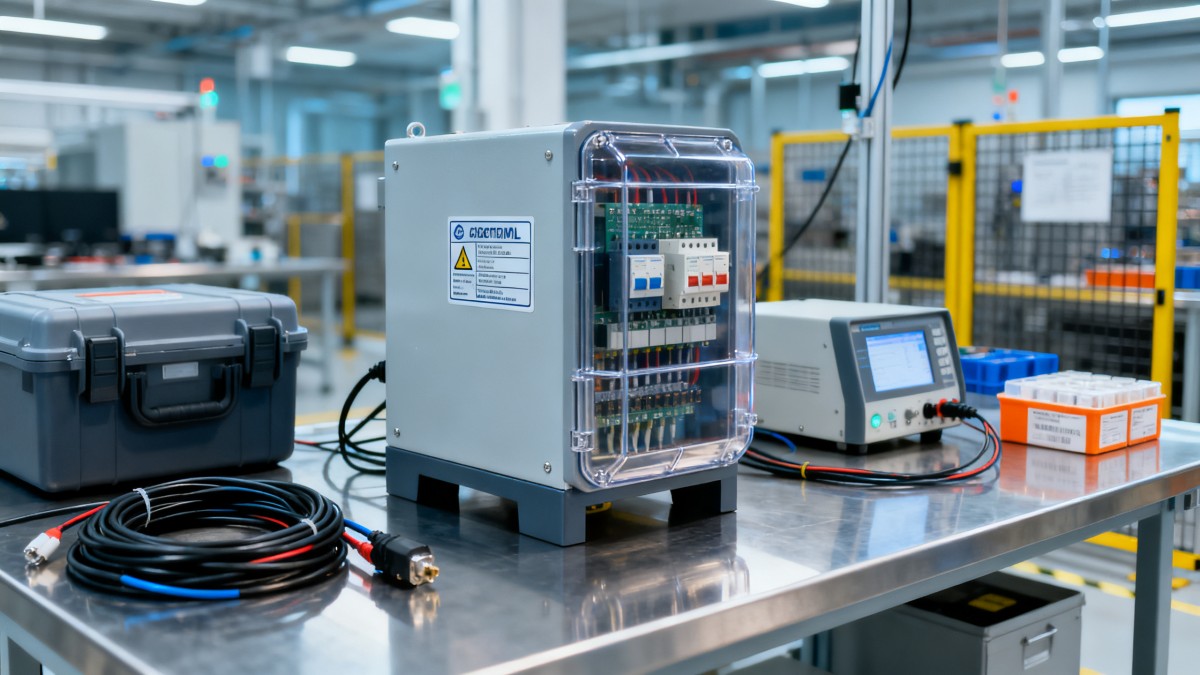
For incoming inspection, teams should verify that physical markings match approved documents. Check model number, serial or batch traceability, certification label details, electrical ratings, hazardous area classification where applicable, ingress protection, and any mandatory warnings. If the delivered product differs from approved documentation, hold release until the difference is formally assessed.
Risk-based prioritization helps when resources are limited. High-risk products such as electrical protection devices, emergency systems, machine safety components, access control systems for critical zones, and equipment used in explosive or high-temperature environments should receive deeper review than low-risk accessories. The principle is simple: the greater the consequence of failure, the stronger the acceptance evidence required.
What evidence gives buyers and inspectors real confidence
From an acceptance standpoint, the strongest evidence is specific, current, and independently verifiable. Third-party certification from a recognized body generally carries more weight than self-declaration, although self-declaration may still be valid in some regulatory frameworks when properly supported. What matters is whether the evidence stands up to audit, inspection, and incident review.
A robust acceptance package usually includes a certificate tied to the exact product, a declaration that references the applicable directives or standards, detailed technical documentation, and installation instructions that clearly state limitations and conditions of safe use. Where required, factory audit status or ongoing surveillance records can further improve confidence.
Traceability is equally important. Quality teams should be able to link the accepted item to a production batch, material record, or serial identifier. Without traceability, post-installation investigation becomes difficult, and recall management becomes more costly. For critical industrial assets, poor traceability can be treated as a safety weakness in itself.
Buyers should also pay attention to test context. A report is more useful when it shows test method, edition level, pass criteria, operating conditions, and product configuration. Summary statements without technical detail may look reassuring, but they rarely help when a product is challenged by a client, regulator, or insurer.
How Security & Safety standards create business value beyond compliance
Although product acceptance is the immediate concern, strong alignment with Security & Safety standards delivers wider business benefits. It reduces rework, prevents shipment holds, shortens approval cycles, and lowers the risk of costly field modifications. For EPC contractors and facility operators, this directly affects project schedule reliability and commissioning efficiency.
For safety managers, compliant products support incident prevention and defensible risk management. If an event occurs, the organization must show that it selected equipment according to recognized standards and performed reasonable verification. Weak acceptance controls can become a major liability issue after an accident, especially where human safety or public infrastructure is involved.
For procurement leaders, standards-backed products can improve total cost of ownership even when unit price is higher. The savings come from fewer delays, lower inspection friction, less documentation rework, reduced maintenance risk, and stronger acceptance by authorities and end users. In high-consequence industries, the cheapest noncompliant option is often the most expensive decision over the asset lifecycle.
There is also a trust dimension. Suppliers that consistently provide transparent, standard-aligned, well-documented products are easier to qualify and retain. Over time, this improves sourcing resilience because the buyer spends less effort resolving preventable compliance disputes and more effort on strategic quality improvement.
A practical acceptance checklist for quality control and safety managers
Before approving any industrial product in the Security & Safety category, confirm the applicable regional and project-specific standards. Verify whether the requirement is legal, contractual, insurer-driven, or site-specific. Do not assume that a globally sold product is universally acceptable.
Request and review the full compliance package. Confirm that the certification or declaration applies to the exact model and configuration being supplied. Check edition dates, issuing bodies, product ratings, environmental limitations, and any conditions of safe installation or use.
Inspect product markings and labels against documents. Ensure consistency across nameplate, manual, packaging, and certification references. If a discrepancy exists, escalate it before installation rather than treating it as an administrative issue.
Assess field suitability. Confirm that the certified product is appropriate for the real operating environment, including temperature, ingress, vibration, EMC exposure, hazardous area classification, fire expectations, and maintenance access conditions. Formal compliance is necessary, but contextual suitability is what prevents failure.
Document the acceptance decision. Maintain clear records of reviewed standards, evidence accepted, deviations noted, and approval basis. Good records support audit readiness, warranty claims, incident defense, and future procurement consistency.
Conclusion: product acceptance depends on verified alignment, not assumed compliance
Security & Safety standards affect product acceptance because they define whether equipment is legally acceptable, technically suitable, and operationally safe in the environment where it will be used. For quality control and safety managers, the central task is not collecting the longest list of standards. It is identifying the standards that truly govern the application, validating credible evidence, and confirming that the delivered product matches the approved basis.
The most reliable acceptance decisions come from a disciplined process: define requirements early, verify documentation deeply, inspect physical traceability carefully, and assess real-world use conditions before release. When that process is followed, Security & Safety standards become more than a compliance burden. They become a practical tool for preventing rejection, reducing operational risk, and protecting long-term asset reliability.
Technical Specifications
- SASO Mandates Dual Energy Label for Industrial Transformers in Saudi Arabia from May 2026Author :Grid Infrastructure Analyst
- EN 61000-4-30:2026 Enforced: Class A Harmonic Traceability Mandatory for EU PQ AnalyzersAuthor :Precision Metrology Expert
- US DOE Level 3 Transformer Efficiency Standard Effective July 1, 2026Author :Grid Infrastructure Analyst
Expert Insights

Chief Security Architect
Dr. Thorne specializes in the intersection of structural engineering and digital resilience. He has advised three G7 governments on industrial infrastructure security.
Related Analysis
- May 06, 2026SASO Mandates Dual Energy Label for Industrial Transformers in Saudi Arabia from May 2026Author :Grid Infrastructure Analyst
- May 06, 2026EN 61000-4-30:2026 Enforced: Class A Harmonic Traceability Mandatory for EU PQ AnalyzersAuthor :Precision Metrology Expert
- May 06, 2026US DOE Level 3 Transformer Efficiency Standard Effective July 1, 2026Author :Grid Infrastructure Analyst
Core Sector // 01
Security & Safety