Security & Safety Standards That Often Get Missed in Expansion Projects
Author
Date Published
Reading Time

Expansion projects often focus on speed, scope, and budget, while critical Security & Safety standards are overlooked until they trigger delays, compliance gaps, or operational risk. For project managers and engineering leads, knowing which requirements are commonly missed is essential to protecting people, assets, and long-term performance. This article highlights the blind spots that can compromise industrial expansion and explains how to address them early.
Why do Security & Safety standards get missed so often in expansion projects?
In most industrial expansion programs, teams are under pressure to add capacity fast, connect new equipment to existing utilities, and keep production downtime as short as possible. That pressure creates a predictable pattern: design decisions are locked before risk reviews are fully mature, procurement begins before compliance mapping is complete, and contractors interpret requirements differently across regions. As a result, important Security & Safety standards are treated as a final inspection issue instead of a design input.
Another reason is that expansion work is rarely a clean-sheet project. Brownfield environments involve legacy systems, mixed documentation quality, outdated drawings, and inherited hazards. A new fire alarm loop may interact with an old control panel. A new access point may weaken perimeter control. A ventilation upgrade may alter hazardous area classifications. Even when companies understand major codes, they can still miss the interfaces between old and new systems, which is where many Security & Safety standards failures emerge.
For project managers, the practical lesson is simple: missed standards are usually not caused by a lack of awareness alone. They are caused by fragmented ownership, weak early-stage coordination, and assumptions that compliance can be “checked later.” In heavy industry, that assumption is expensive.
Which Security & Safety standards are most commonly overlooked during expansion?
The most commonly missed requirements are not always the most technical ones. They are often the cross-functional standards that sit between engineering, operations, procurement, and EHS teams. Project leaders should pay special attention to the following areas.
- Functional safety integration: Safety instrumented functions, interlocks, emergency shutdown logic, proof test intervals, and SIL assumptions may be copied from older units without validating changed operating conditions.
- Fire and life safety coordination: Detection, alarm zoning, suppression coverage, firewater adequacy, egress paths, and occupancy changes are frequently reviewed too late.
- Hazardous area classification updates: New process equipment, cable entries, ventilation changes, and temporary enclosures can alter area classifications and equipment selection requirements.
- Electrical protection compliance: Arc flash studies, grounding continuity, selective coordination, panel labeling, and short-circuit capacity checks are often incomplete after system expansion.
- Machine guarding and access control: New conveyors, skids, robotics, and maintenance platforms may create pinch points or bypass opportunities that were not present in the original layout.
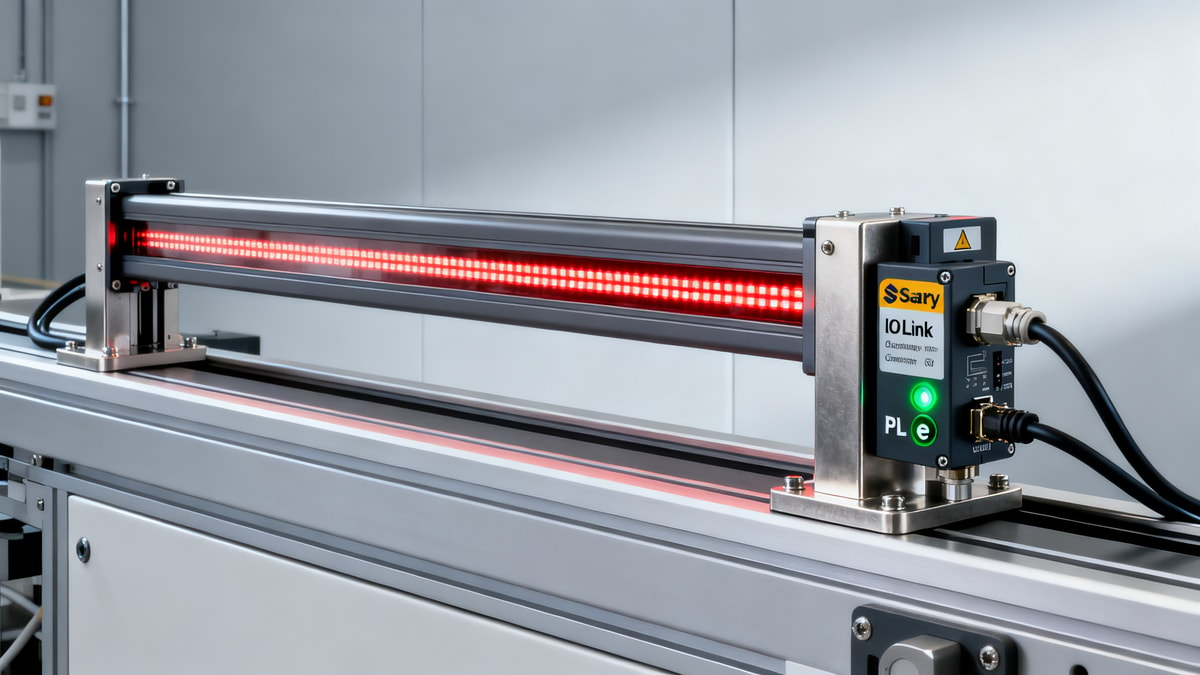
- Cyber-physical security: Expansion projects increasingly connect OT assets, remote monitoring tools, and smart instruments, but network segmentation and access governance may lag behind.
These missed Security & Safety standards matter because each one affects commissioning, insurance, authority approvals, and long-term reliability. In global projects, teams must also verify whether local code, customer specification, insurer requirement, and international standards align or conflict.

How can project managers tell whether a “compliant design” is actually incomplete?
A common mistake is assuming that a package is compliant because each vendor has provided certificates for its own equipment. Equipment compliance does not automatically mean system compliance. A certified detector, breaker, valve, or enclosure may still be wrongly located, poorly integrated, or unsuited to the operating environment. Project managers should therefore look for evidence that Security & Safety standards have been verified at the system level.
There are several warning signs. One is when hazard reviews focus only on the new equipment and not on upstream or downstream impacts. Another is when procurement documents reference standards generally but do not define testing, documentation, witness points, or acceptance criteria. A third is when the project schedule places key validation activities after mechanical completion, leaving little room for redesign.
Strong projects ask better questions early. Has a management of change process been triggered? Have escape routes changed because of new structures or equipment footprints? Will the added electrical load alter protection settings? Does the expansion change maintenance access, lifting plans, or emergency response timing? If those questions do not have clear owners and documented answers, the design may be incomplete even if drawings look finished.
What are the biggest differences between greenfield and brownfield Security & Safety standards risks?
Greenfield projects start with more design freedom, so the challenge is usually building a complete compliance framework from the ground up. Brownfield expansion is harder in a different way: the project must preserve live operations while introducing change into an existing risk environment. For most project management teams, brownfield conditions create the greater chance of overlooked Security & Safety standards.
In greenfield settings, teams can align layout, utilities, fire strategy, zoning, and access control from the earliest phases. In brownfield work, they inherit constraints such as undersized cable routes, obsolete switchgear, undocumented bypasses, and legacy emergency systems. A new process line may technically comply on paper, but once tied into an old plant, hidden interfaces appear. Those interfaces can affect alarm philosophy, evacuation timing, pressure relief assumptions, and operator visibility.
This difference has direct implications for execution. Brownfield projects require more site verification, more interface management, and stronger temporary risk controls during construction and cutover. They also need more disciplined documentation turnover, because the final risk profile depends on what was actually installed, not what was originally intended.
Which checks should be completed before procurement and contractor mobilization?
If Security & Safety standards are reviewed only after purchase orders are issued, teams lose leverage. Before procurement starts, project leaders should define a practical compliance baseline covering design, materials, installation, testing, and operations handover. This does not mean freezing every detail, but it does mean preventing avoidable ambiguity.
This table is especially useful for EPC teams and owner representatives because it translates broad Security & Safety standards into procurement-ready controls. Once these checkpoints are embedded in contracts and bid packages, compliance becomes easier to measure.
What costly misconceptions cause Security & Safety standards failures during execution?
One misconception is that certification labels alone guarantee safe operation. They do not. A compliant device installed in the wrong hazardous zone or under the wrong temperature class can still create risk. Another misconception is that “same as existing” is a safe design basis. Existing installations may be grandfathered, undocumented, or no longer aligned with current requirements.
A third misconception is that safety and security can be separated neatly. In modern industrial sites, they often overlap. Access control influences emergency response. Network architecture affects alarm availability and remote shutdown integrity. Visitor management can affect contractor safety accountability. When these interfaces are ignored, the project may pass a narrow discipline review yet still underperform in real operations.
Project teams also underestimate the impact of undocumented field changes. A moved detector, a substituted cable gland, an extra door, or a temporary bypass can undermine the original basis of design. That is why walkdowns, redline control, and pre-startup verification are not administrative burdens; they are core mechanisms for preserving Security & Safety standards in the field.
How should teams balance cost, schedule, and Security & Safety standards without overengineering?
Good compliance is not the same as excessive design. The goal is to apply Security & Safety standards based on actual risk, operating conditions, and lifecycle consequences. Overengineering adds cost, but underdefining requirements creates rework, delays, and exposure that usually cost more. The right balance comes from prioritization.
Start by identifying high-consequence interfaces: live tie-ins, hazardous area boundaries, emergency shutdown logic, firewater demand, operator access, confined spaces, and OT connectivity. These are the areas where modest early investment in analysis, testing, and review prevents major disruption later. Then separate mandatory compliance requirements from optional preferences. This helps procurement compare bids realistically and reduces contractor interpretation gaps.
It is also wise to evaluate lifecycle costs instead of purchase price alone. A lower-cost component with weak certification support, limited traceability, or poor service documentation can create long-term risk. For industrial buyers and project managers, durable compliance evidence is often more valuable than nominal upfront savings.
What should be verified before commissioning and handover?
Late-stage project pressure often drives teams to treat handover as a paperwork milestone. That is dangerous. Before commissioning, Security & Safety standards must be verified through documentation, physical inspection, and functional testing. Drawings should reflect installed conditions. Safety-critical devices should be tagged consistently. Cause-and-effect logic should be tested against real sequences, not just simulated assumptions.
Teams should also confirm that operations personnel are ready to manage the expanded facility. That includes updated procedures, lockout-tagout boundaries, emergency response maps, maintenance instructions, spare parts strategy, and training records. Many sites technically complete construction but remain operationally vulnerable because the organization is not prepared for the new risk profile.
A strong handover package should include as-built drawings, inspection records, test certificates, deviation logs, residual risk notes, and clear ownership of post-startup actions. Without that package, compliance becomes difficult to sustain and audit.
What are the most useful takeaways for project managers and engineering leads?
The most missed Security & Safety standards in expansion projects are usually hidden in interfaces, not in obvious equipment specs. Project leaders should focus on integration, field changes, brownfield constraints, and system-level validation. Early standards mapping, disciplined management of change, and procurement documents with explicit compliance deliverables can reduce both risk and delay.
For organizations operating across multiple countries or contractor networks, consistency matters even more. Standards should be translated into review checkpoints, bid requirements, and handover evidence that every stakeholder can understand. That approach strengthens trust, improves audit readiness, and supports safer long-term operations.
If you need to confirm a specific expansion strategy, supplier capability, compliance pathway, project timeline, or sourcing decision, the best starting questions are: which Security & Safety standards apply to this site and jurisdiction, what interfaces with existing systems create the highest risk, what evidence must vendors provide before award, and what testing must be completed before startup approval. Those questions will surface problems early, when they are still affordable to solve.
Technical Specifications
- US DOE Level 3 Transformer Efficiency Rule Takes Effect July 1, 2026Author :Grid Infrastructure Analyst
- INMETRO Proposes EMP Immunity Requirement for Industrial Laser Distance Meters in BrazilAuthor :Precision Metrology Expert
- Indonesia BPOM Fast-Tracks Chinese Industrial Air PurifiersAuthor :Environmental Engineering Director
Expert Insights

Chief Security Architect
Dr. Thorne specializes in the intersection of structural engineering and digital resilience. He has advised three G7 governments on industrial infrastructure security.
Related Analysis
- May 05, 2026US DOE Level 3 Transformer Efficiency Rule Takes Effect July 1, 2026Author :Grid Infrastructure Analyst
- May 05, 2026INMETRO Proposes EMP Immunity Requirement for Industrial Laser Distance Meters in BrazilAuthor :Precision Metrology Expert
- May 05, 2026Indonesia BPOM Fast-Tracks Chinese Industrial Air PurifiersAuthor :Environmental Engineering Director
Core Sector // 01
Security & Safety