SASO Extends AI Water Module Cybersecurity Deadline to Oct 2026
Author
Date Published
Reading Time

Saudi Arabia’s Standards, Metrology and Quality Organization (SASO) announced on April 28, 2026, a compliance extension for three categories of water treatment IoT devices under the SASO IEC 62443-4-2 cybersecurity framework. This update directly affects exporters and manufacturers of smart water monitoring and control equipment targeting the Saudi market — particularly Chinese IoT device suppliers engaged in water infrastructure projects.
Event Overview
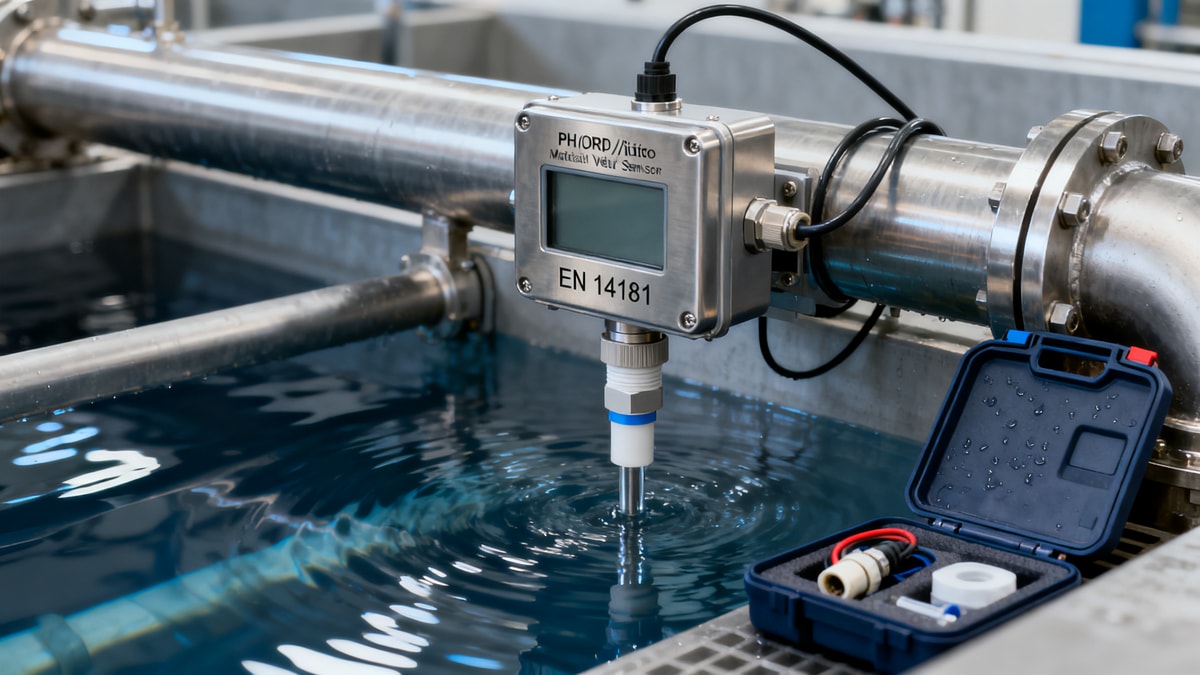
On April 28, 2026, SASO published an official exemption list specifying that intelligent water quality modules — including AI-embedded pH, turbidity, and conductivity transmitters; integrated water purification controllers; and cloud platform gateways — may defer full compliance with SASO SRP (Saudi Product Safety Program) cybersecurity certification requirements until October 31, 2026. The exemption applies specifically to the SASO adoption of IEC 62443-4-2, which governs secure product development lifecycle requirements for industrial automation and control systems.
Which Subsectors Are Affected
Direct Exporters (e.g., Chinese Water IoT Device Manufacturers)
These companies supply AI-enabled water sensors and controllers directly to Saudi importers or EPC contractors. They are affected because the extension does not eliminate the requirement — only postpones it — meaning existing and new shipments must still undergo SASO SRP registration and cybersecurity validation before the October 2026 deadline. Non-compliant units risk customs rejection or market withdrawal post-deadline.
Cloud Platform Providers & SaaS Integrators
Suppliers offering cloud-based water monitoring dashboards or remote management services linked to hardware sold in Saudi Arabia face functional alignment pressure. The exemption explicitly includes ‘cloud platform gateways’, implying that data ingestion, authentication, and firmware update mechanisms must meet local cybersecurity expectations — including potential localization of cloud infrastructure or API endpoints per SASO guidance.
Local Distributors & System Integrators in KSA
Entities responsible for importing, commissioning, or bundling water treatment hardware into turnkey solutions must verify whether their current inventory or pending orders include exempted devices. Since compliance is tied to product model and firmware version, they bear operational responsibility for ensuring traceability and documentation readiness ahead of the October 2026 cutoff.
What Relevant Companies or Practitioners Should Focus On Now
Monitor Official Updates from SASO and SASO-Accredited Bodies
The exemption list is a procedural clarification, not a permanent regulatory change. Companies should track announcements from SASO and its designated conformity assessment bodies (CABs) for updates on accepted test labs, required documentation formats, and possible revisions to the scope — especially regarding AI algorithm transparency or firmware signing protocols.
Prioritize SRP Registration for High-Volume or Flagship Models
Given limited testing capacity and lead times for cybersecurity evaluation, exporters should identify top-selling or project-critical models (e.g., multi-parameter AI transmitters deployed in municipal plants) and initiate SASO SRP registration immediately — even within the extension window — to avoid bottlenecks ahead of the October 2026 deadline.
Assess Cloud Deployment Architecture Against Local Requirements
Analysis shows that SASO’s inclusion of ‘cloud platform gateways’ signals growing scrutiny of data residency and remote access security. Exporters relying on global cloud backends should evaluate whether local cloud hosting (e.g., via AWS Middle East or STC Cloud) or hybrid edge-cloud configurations better align with anticipated implementation expectations — not just certification criteria.
Align Technical Documentation with IEC 62443-4-2 Development Lifecycle Evidence
Observably, SASO’s enforcement focus has shifted toward verifiable secure development practices — not just end-product testing. Companies should ensure their technical files include evidence of threat modeling, secure coding standards, vulnerability management processes, and firmware update integrity controls — all mapped to IEC 62443-4-2 clauses.
Editorial Perspective / Industry Observation
This extension is best understood as a transitional signal — not a relaxation of policy intent. From an industry perspective, SASO is balancing market readiness with strategic digital sovereignty goals: allowing time for vendors to adapt while reinforcing that cybersecurity is non-negotiable for critical water infrastructure. The six-month window reflects recognition of implementation complexity, especially for AI-integrated edge devices where algorithm behavior adds verification overhead. However, the absence of further extensions beyond October 2026 suggests this is likely the final grace period before full enforcement begins.
Current more appropriate interpretation is that SASO is treating cybersecurity compliance as a phased maturity process — first enabling registration, then verifying secure development rigor, and eventually linking certification to ongoing vulnerability disclosure and patching performance. Industry stakeholders should therefore treat the extension not as delay, but as a structured ramp-up phase.

Conclusion
This SASO update marks a concrete step in the formalization of cybersecurity accountability for smart water infrastructure in Saudi Arabia. It does not reduce regulatory expectations — rather, it structures them into a time-bound, actionable pathway. For affected businesses, the key takeaway is not relief, but urgency: the extension provides operational breathing room, not strategic reprieve. The most rational response is to treat the period through October 2026 as a focused implementation sprint — prioritizing documentation, lab engagement, and architecture alignment over waiting for further policy adjustments.
Information Sources
Main source: Official SASO exemption notice published on April 28, 2026, referencing SASO IEC 62443-4-2 implementation. Further details remain subject to confirmation by SASO-accredited conformity assessment bodies and updated guidance documents — these require ongoing monitoring.
Technical Specifications
- Indonesia Opens Bearing & Seal Manufacturing to 100% FDIAuthor :Heavy Industry Strategist
- SASO Extends AI Water Module Cybersecurity Deadline to Oct 2026Author :Environmental Engineering Director
- Copper Price Surges 4.1% to Record High in 2026; Impacts BOM Costs for Cable & Transformer MakersAuthor :Grid Infrastructure Analyst
Expert Insights

Chief Security Architect
Dr. Thorne specializes in the intersection of structural engineering and digital resilience. He has advised three G7 governments on industrial infrastructure security.
Related Analysis
- May 02, 2026Indonesia Opens Bearing & Seal Manufacturing to 100% FDIAuthor :Heavy Industry Strategist
- May 02, 2026SASO Extends AI Water Module Cybersecurity Deadline to Oct 2026Author :Environmental Engineering Director
- May 02, 2026Copper Price Surges 4.1% to Record High in 2026; Impacts BOM Costs for Cable & Transformer MakersAuthor :Grid Infrastructure Analyst
Core Sector // 01
Security & Safety